
5G Network Management: Integrating Service Orchestration For End-to-End Automation
Monitoring, telemetry, assurance, and closed-loop operations
Effective monitoring supplies the data that powers assurance and closed-loop automation. Telemetry sources in U.S. networks typically include performance counters from radio units, flow and latency measurements on transport segments, and resource metrics from cloud and edge platforms. Aggregation and normalization of these telemetry streams enable consistent interpretation across domains; operators often deploy time-series databases and stream processing engines to support real-time analysis and historical trend assessments necessary for SLA verification and capacity planning.
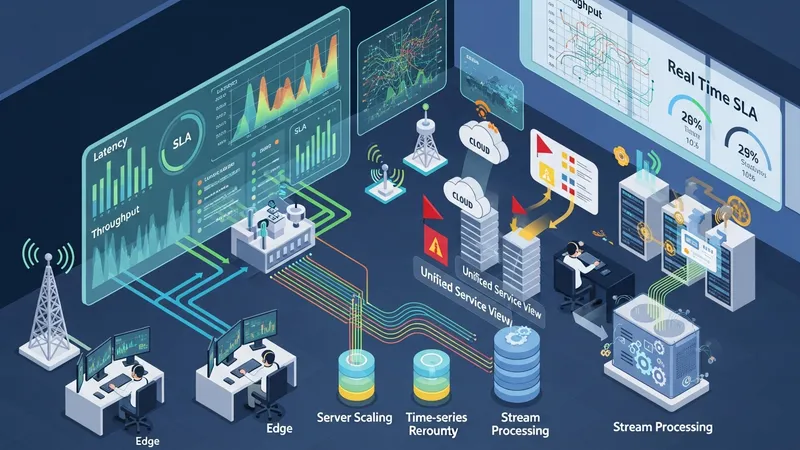
Assurance systems translate monitored indicators into service health assessments and alerts. In U.S. network operations centers, assurance dashboards may combine multi-domain indicators into a unified service view that correlates underlying resource states with service-level metrics. Automated rule sets and anomaly detection models can flag deviations from expected performance, and those detections may trigger orchestration workflows for remediation, such as scaling, rerouting, or reconfiguration of affected components.
Data volume and velocity pose practical challenges; U.S. deployments often handle large-scale telemetry by filtering, sampling, and tiering data to balance operational needs and storage costs. Edge aggregation points can pre-process telemetry to reduce upstream load, while longer-term storage may retain aggregated or summarized indicators for trend analysis. Careful design of telemetry schemas and retention policies helps ensure that assurance systems remain responsive and cost-manageable.
Privacy and security of telemetry are also operational considerations. In the United States, operators may follow sector guidance and internal policies for data handling, access control, and retention. Encryption in transit, role-based access to assurance tools, and auditability of automation triggers are commonly included as defensive measures. These controls help ensure that closed-loop actions rely on trusted data and that any automated changes remain accountable within operational governance frameworks.